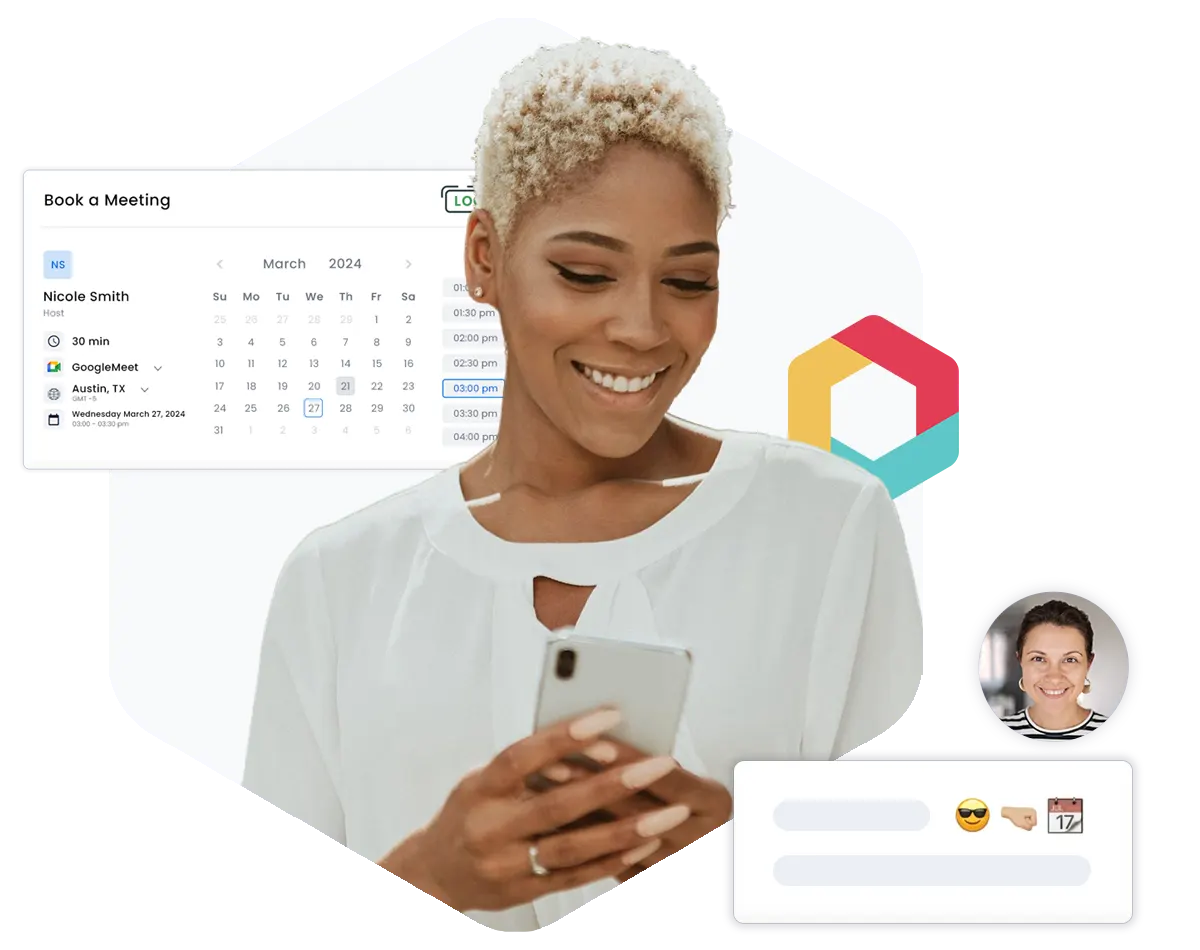
Add automated appointment scheduling to any website, email, text, chat, social media or Salesforce Community. Optimize your sales funnel & close deals faster.
Add appointment scheduling as a call to action anywhere you have an online presence; websites, Salesforce Communities, social media sites and more. - Auto-create leads/contacts in Salesforce and securely capture valuable customer information.
Read moreBook meetings in real time directly in Salesforce. Find a resource, available time slot, and book it.
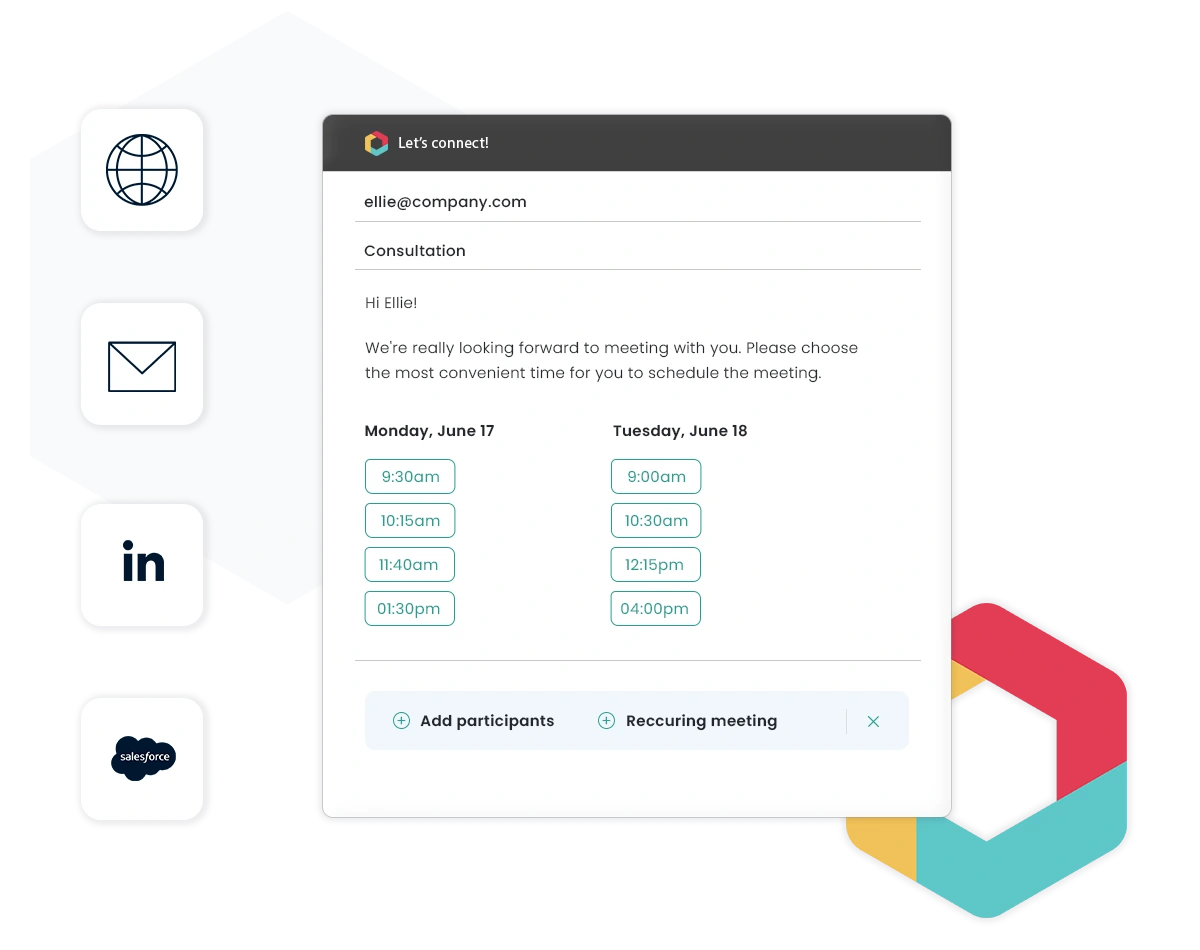
Read moreSend customized meeting invitations directly from Salesforce or create meeting links for one-click scheduling - Add scheduling tools to any object, community or case.
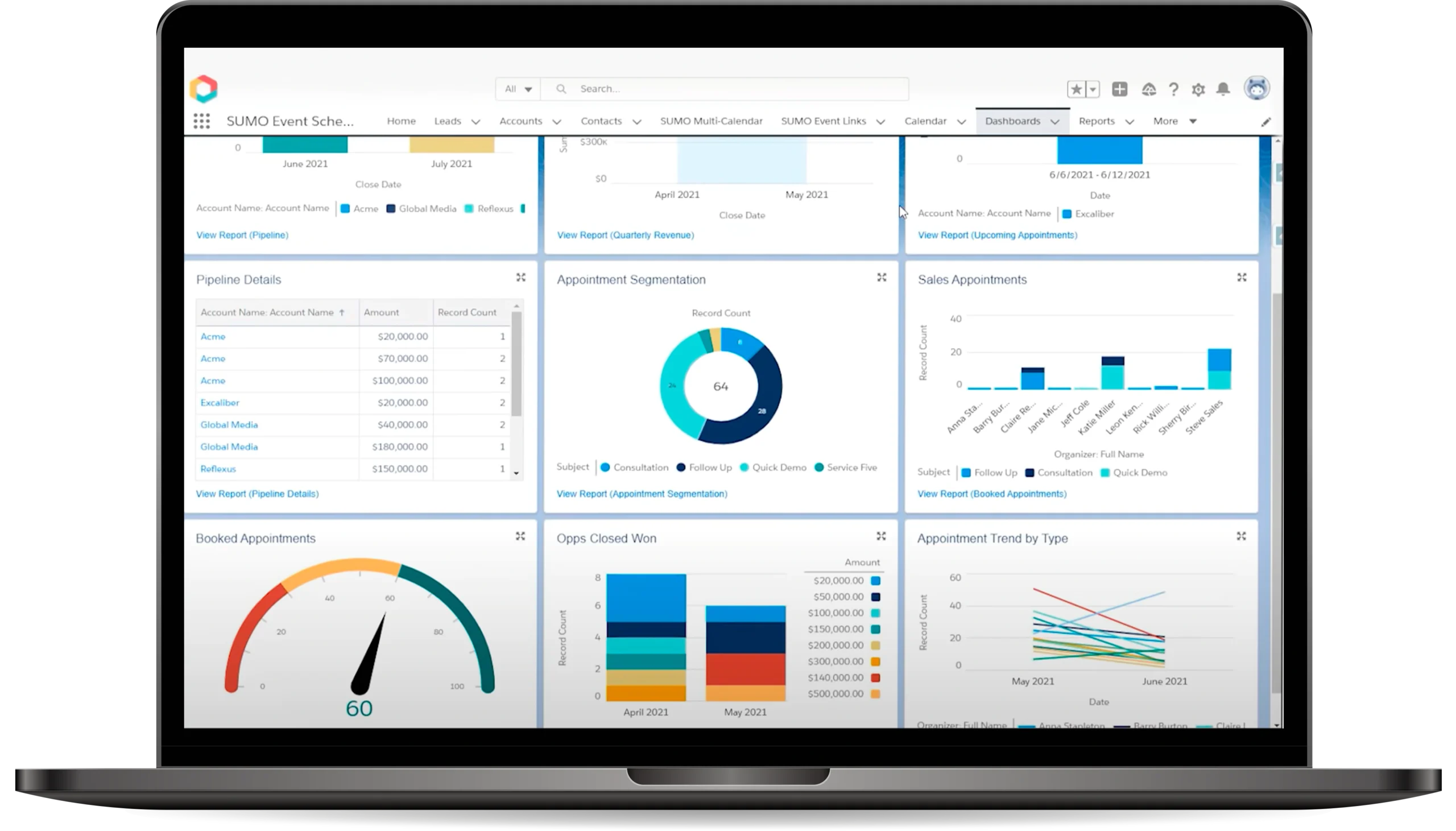
Read moreMake better data-driven business decisions with Salesforce native reports and dashboards.
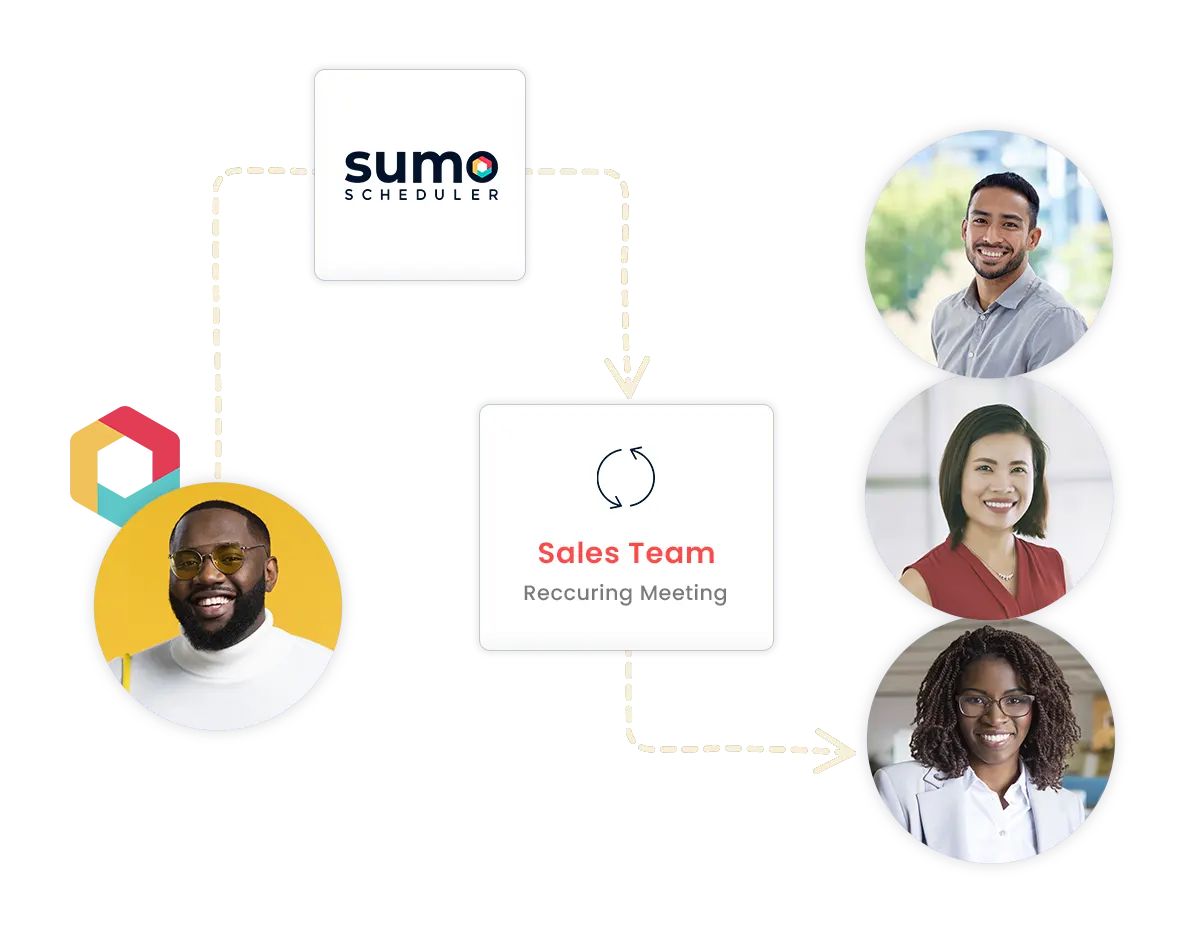
Read moreEnsure prospects meet with the right staff member, at the right location and time.
Read moreReduce no-shows by >27%. Automated emails and text messages, ensure everyone shows up on time or can reschedule at their convenience.
Read moreIntegrate scheduling with existing technologies. - At the core of SUMO is a Calendar API that maintains a secure persistent connection to standard calendar platforms.
Read more